Challenge logins from new country or device
Make sure your user accounts are as secure as possible.
As a part of the measures for protecting your users against account takeovers, you can choose to activate step-up authentication, whenever the user shows behavior outside normal. Step-up verification can be anything that requires the user to prove that they own the account, like e.g. multi-factor authentication or a simple E-mail verification.
In this guide you will set up Castle to return a challenge response whenever a user logs in from a new country or device. Once the user has passed the extra verification, they will be added to an allow list to prevent from being challenged repeatedly.
Adjust what is suspicious for your businessIn this tutorial you will learn how to set up policies to challenge users logging in from a new device or from a new country. However this is only an example: we encourage you to adjust the policy to challenge user to the needs of your business.
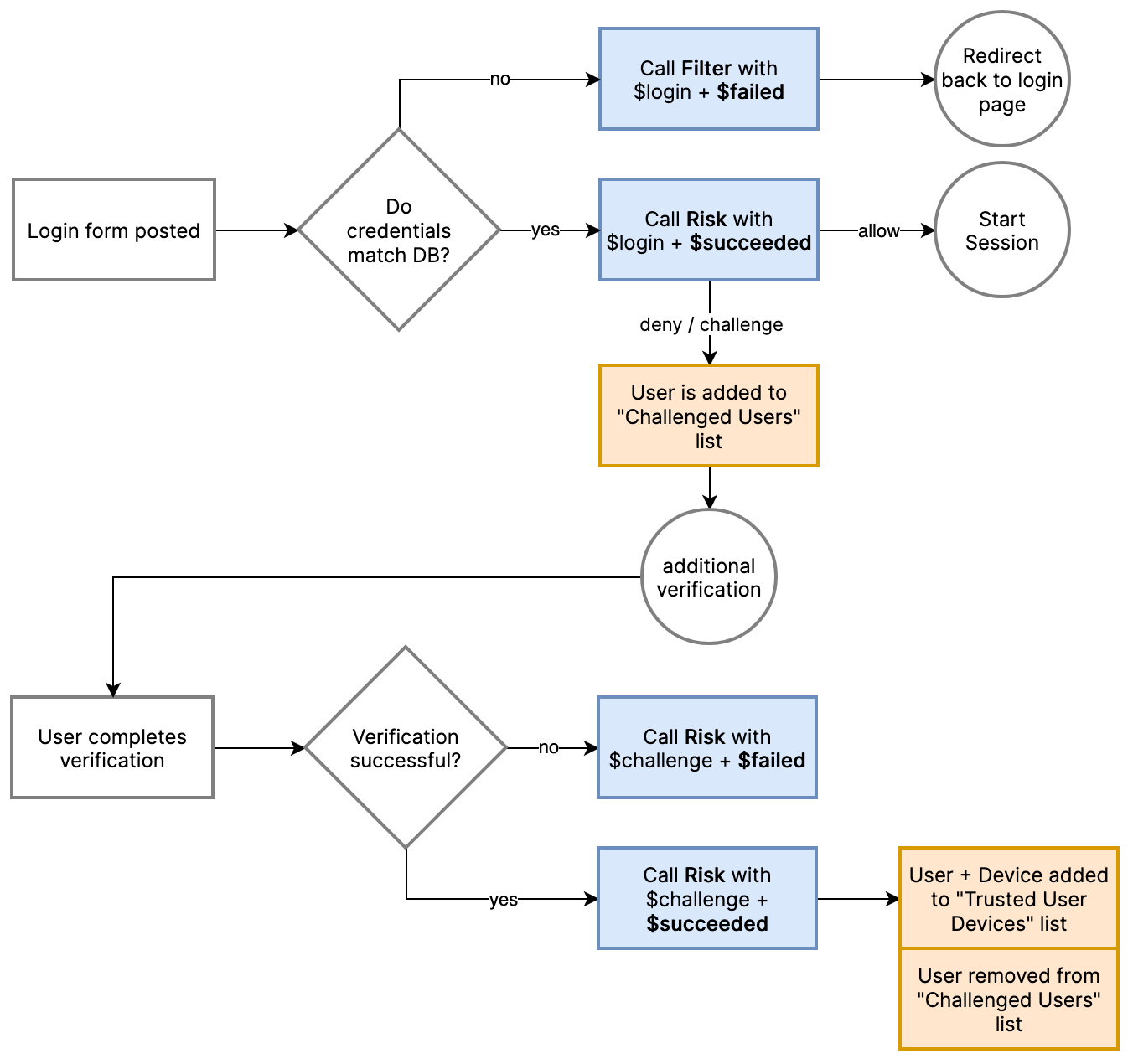
Overview of the challenge flow at login
Step 1. Create required lists
First, head over to the lists management page and create two new lists that will hold challenged and trusted devices of a user:
List Name | Primary Entity | Secondary Entity | Auto-archivation time |
|---|---|---|---|
Challenged Devices | User ID | Device Fingerprint | |
Trusted User Devices | User ID | Device Fingerprint | 20160 minutes (14 days) |
From the Trusted User Devices list, we'll set the default auto-archivation to 14 days (14 × 24 × 60 = 20160 minutes), but depending on your requirements you may choose to shorten/increase this.
Step 2. Create the policies
Now configure four new policies from the policies page. The order of policies matters, so make sure to reorder them properly if needed:
Event name: Login Succeeded
Order | Policy Name | Trigger | Actions |
|---|---|---|---|
1 | Allow trusted device logins | List matches Trusted User Devices |
|
2 | Challenge devices in list | List matches Challenged Devices |
|
3 | Challenge new device or country | Signals is one of |
|
Event name: Challenge Succeeded
Order | Policy Name | Trigger | Actions |
|---|---|---|---|
1 | Trust device on challenge | No condition |
|
Enable your new policiesAfter creating policies you need to remember to enable them. Otherwise your new flow will not work.
Summary
Your app just became more secure while lowering the user friction to the required minimum!
Updated 6 months ago